ICS/OT Cybersecurity controls
Cyber-Physical & ICS/OT Security
Industrial Control Systems (ICS) and Operational Technology (OT) environments are becoming increasingly interconnected as organisations adopt digital transformation, remote operations, and data-driven optimisation. While this connectivity delivers significant operational benefits, it also introduces cyber risk into systems that directly control physical processes. Unlike traditional IT environments, cyber incidents in ICS and OT can impact safety, production, environmental outcomes, and business continuity, making cyber-physical security a critical business and operational concern.
Effective ICS/OT security requires more than applying traditional IT controls. These environments often include legacy systems, proprietary protocols, and operational constraints where availability and safety are paramount. A structured, risk-based approach is essential—one that begins with discovery and visibility, and progressively matures through secure access, risk-based vulnerability management, defensible architecture, and operationally aligned incident response. This approach enables organisations to reduce cyber risk while maintaining safe and reliable operations.
Industry, Regulation, and Critical Infrastructure Considerations
ICS/OT security requirements vary significantly across industries such as energy, utilities, manufacturing, and transport, each with its own operational models, threat landscape, and regulatory obligations. Organisations operating within regulated or critical infrastructure sectors must align cyber security controls with industry-specific standards, safety requirements, and compliance frameworks. Where environments fall under critical infrastructure definitions, cyber security solutions must be tailored to address heightened risk, regulatory scrutiny, and national resilience expectations rather than relying on generic security approaches.
A one-size-fits-all model does not work for ICS environments. Security controls, architecture, and response capabilities must be designed to reflect industry context, asset criticality, and operational impact. Tailoring solutions ensures cyber risk is reduced in a way that supports compliance, protects essential services, and aligns with both operational and regulatory expectations.
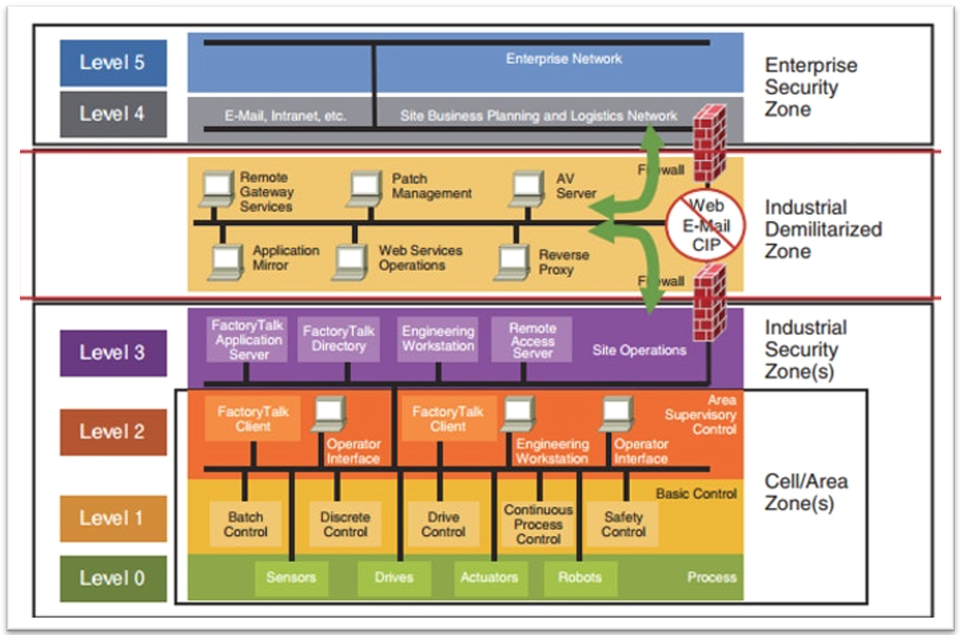
Alignment with IEC 62443 – Zones, Conduits, and the Purdue Model
Our approach to ICS and OT security is aligned with the IEC 62443 framework, using the concepts of zones and conduits together with the Purdue Model to establish a defensible and structured security architecture. The Purdue Model provides a logical separation between enterprise systems, operational systems, and control processes, while IEC 62443 defines how assets within these layers can be grouped into zones based on risk and function, with conduits used to securely manage communication between them.
By applying zones and conduits across Purdue levels, organisations can clearly define trust boundaries, control data flows, and reduce unnecessary exposure between IT and OT environments. This layered approach limits attack pathways, helps contain cyber incidents, and supports consistent enforcement of security controls without disrupting operational requirements. It also provides a scalable foundation for improving cyber maturity over time, enabling organisations to move from flat, high-risk networks to resilient architectures aligned with industry standards and regulatory expectations.
Why ICS Security Is Different
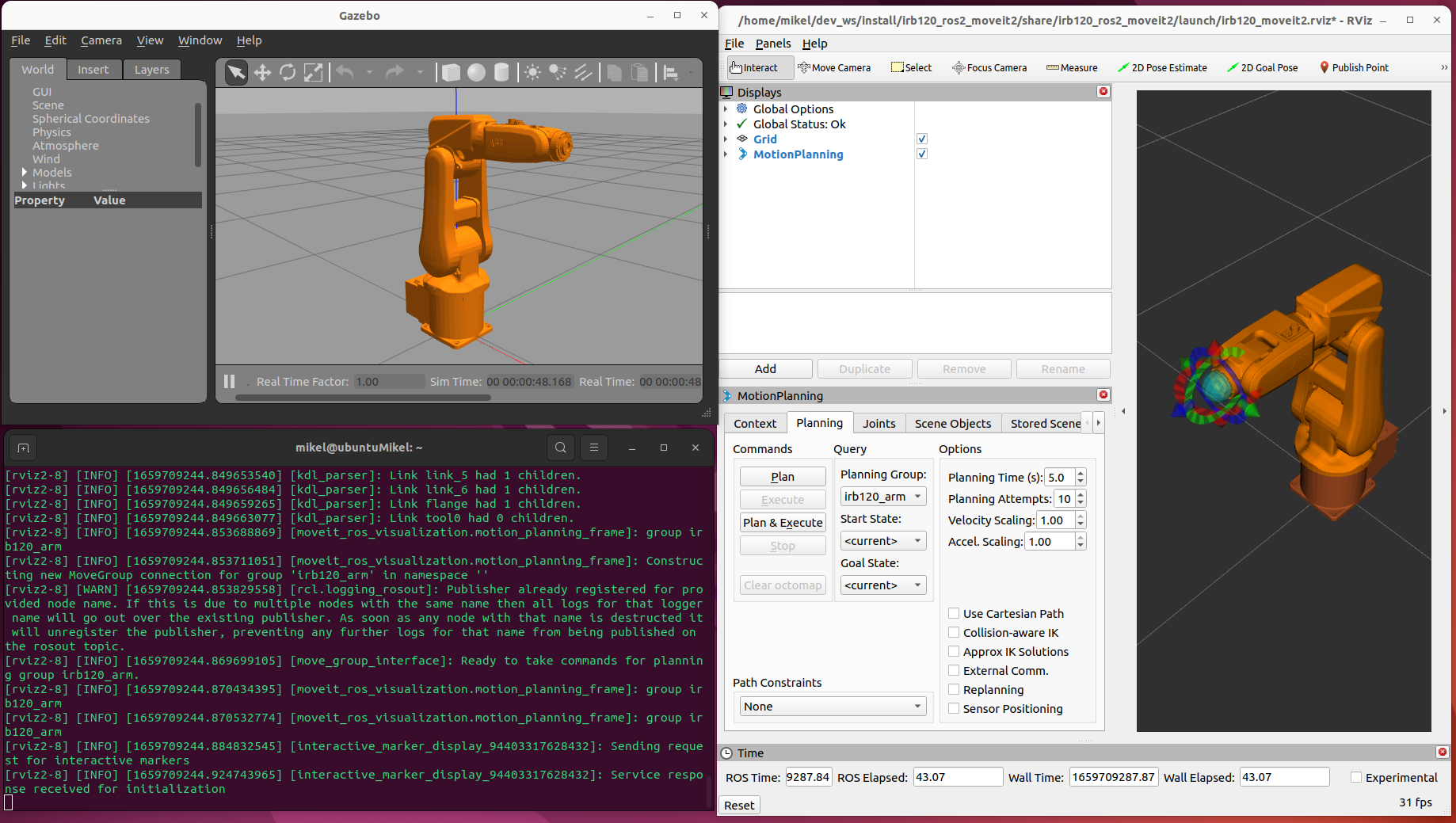
ICS and OT environments present unique challenges that distinguish them from traditional IT systems. These environments control physical processes, often operate continuously, and are designed for longevity rather than frequent change. Applying IT-centric security measures without understanding operational constraints can introduce safety risks, unplanned downtime, or equipment damage.
Effective ICS security must prioritise safety, availability, and reliability while managing cyber risk in a controlled and practical manner. It requires close collaboration between cyber security, engineering, and operations teams, as well as solutions that respect legacy systems and real-world constraints. By recognising these differences, organisations can implement cyber security measures that genuinely reduce risk while supporting safe, resilient, and uninterrupted operations.