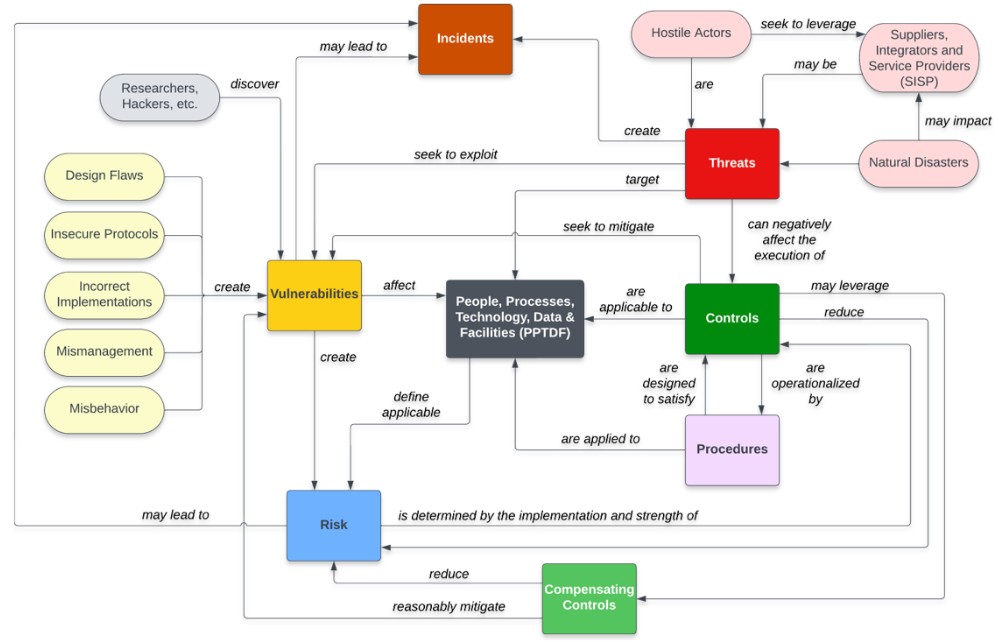
Risks vs Threats vs Vulnerabilities
Risks, threats and vulnerabilities are commonly misunderstood. Fundamentally, vulnerability and risk management practices exist to achieve a minimum level of protection for an organization, which equates to a reduction in the total risk due to the protections offered by implemented controls. This can be conceptualized as a "risk management ecosystem" as it pertains to an organization's overall cybersecurity & data protection efforts. These ecosystem components have unique meanings that need to be understood to reasonably protect people, processes, technology and data, as shown below:
How Risk Management Is Done
Our approach combines structured assessments, risk-based prioritisation, and practical controls to reduce cyber risk to acceptable levels. Starting with discovery and visibility, we identify vulnerabilities, evaluate potential impacts, and assess readiness and compliance gaps. Solutions and controls are then implemented strategically, allowing organisations to optimise security spending while achieving measurable risk reduction.
Assessment - A foundation for reducing and governing cyber risk across IT and OT
Discovery & Asset Inventory
Discovery and asset inventory establish a complete understanding of all IT and OT assets, including systems, devices, software, users, network connections, and data flows. This process identifies known and unknown assets, third-party connections, and critical dependencies that directly influence cyber risk exposure.
By creating a trusted and continuously relevant asset baseline, organisations gain the visibility required to make informed security, operational, and investment decisions. This assessment forms the foundation for all risk, vulnerability, and architecture activities and supports accurate prioritisation across complex environments.
Risk Assessment
The full risk assessment evaluates cyber threats, vulnerabilities, and potential impacts across IT and OT environments in a structured and consistent manner. Risks are analysed in the context of business objectives, operational continuity, safety, regulatory exposure, and financial impact.
This approach ensures cyber risk is understood in terms that resonate with executives and operational leaders. The outcome is a prioritised risk register aligned to organisational risk appetite, enabling informed decisions on where controls, investment, and governance are most effective.
Vulnerability Assessment
Vulnerability assessments identify weaknesses across operating systems, applications, network devices, and OT platforms while accounting for operational constraints and system criticality. Unlike traditional scanning-only approaches, findings are evaluated in the context of exploitability, exposure, and business impact.
This enables remediation efforts to focus on vulnerabilities that present the greatest risk rather than attempting to address every technical issue. The result is a practical, risk-based remediation roadmap that balances security improvement with operational stability.
Architecture Assessment
Architecture assessments review the design and implementation of network segmentation, access controls, trust boundaries, and security mechanisms across IT and OT environments. This assessment identifies structural weaknesses that could enable lateral movement, unauthorised access, or loss of operational control.
Recommendations focus on improving resilience through defensible architecture, aligned with industry best practices such as the Purdue Model and IEC 62443 principles. The outcome is a clearer, more secure system design that reduces systemic risk and improves long-term maintainability.
Readiness Assessment
Readiness assessments measure how prepared the organisation is to detect, respond to, and recover from cyber incidents affecting IT and OT systems. This includes evaluating incident response plans, roles and responsibilities, escalation paths, communication processes, and technical capabilities.
By identifying gaps before an incident occurs, organisations can strengthen coordination between IT, OT, and business teams. This assessment improves confidence in response capability, reduces downtime, and supports safer, more effective incident management during high-pressure situations.
Compliance & Governance Gap Analysis
Compliance and governance gap analysis evaluates policies, standards, procedures, and oversight mechanisms against recognised frameworks and regulatory obligations. This assessment identifies gaps in accountability, documentation, control ownership, and decision-making structures.
Strengthening governance ensures cyber risk is managed consistently and sustainably over time. The outcome supports audit readiness, regulatory confidence, and clear executive oversight while embedding cyber risk management into broader organisational governance.
Get In Touch